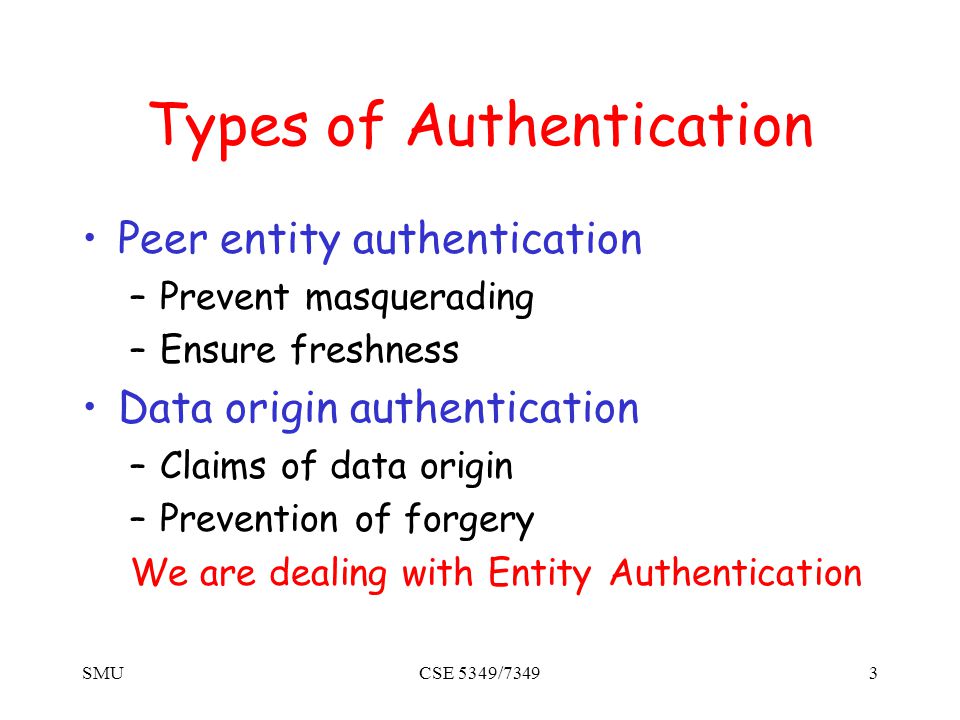
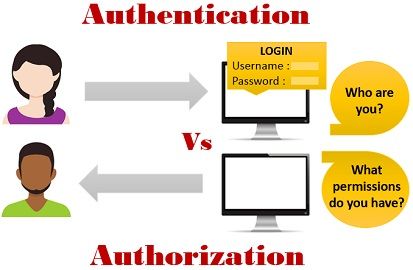
SMUCSE 5349/73491 Authentication Protocols. SMUCSE 5349/73492 The Premise How do we use perfect cryptographic mechanisms (signatures, public-key and symmetric. - ppt download
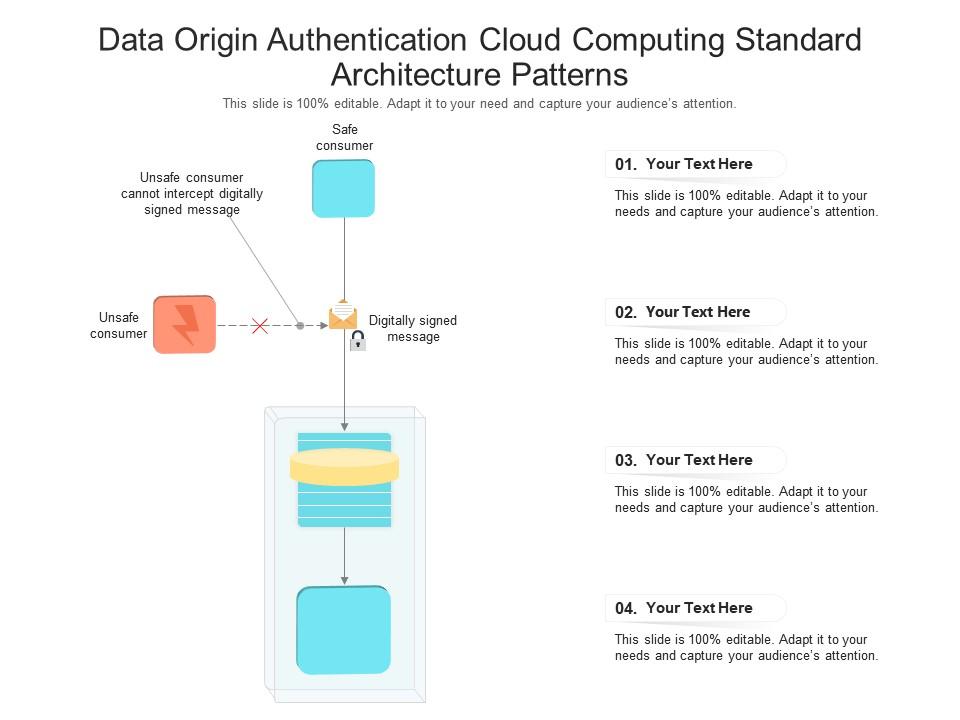
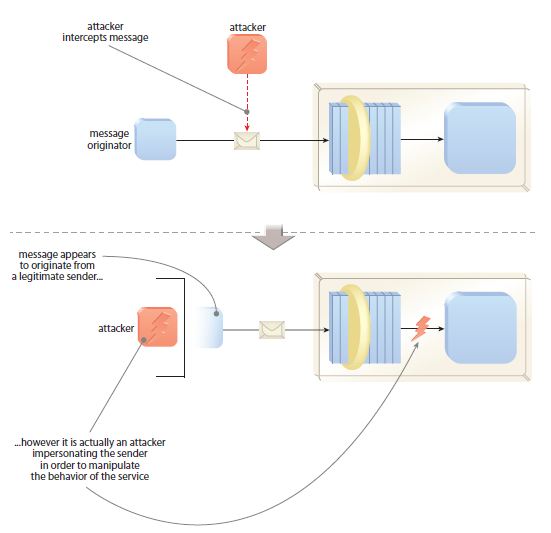
Data Origin Authentication Cloud Computing Standard Architecture Patterns Ppt Presentation Diagram | Presentation Graphics | Presentation PowerPoint Example | Slide Templates








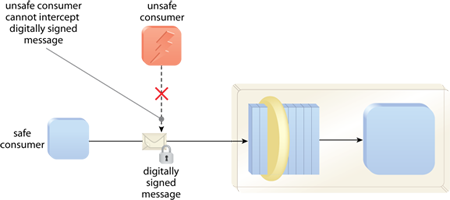
![MS-AUTHSOD]: Data Origin Authentication (Signing) | Microsoft Learn MS-AUTHSOD]: Data Origin Authentication (Signing) | Microsoft Learn](https://learn.microsoft.com/en-us/openspecs/windows_protocols/ms-authsod/ms-authsod_files/image027.png)