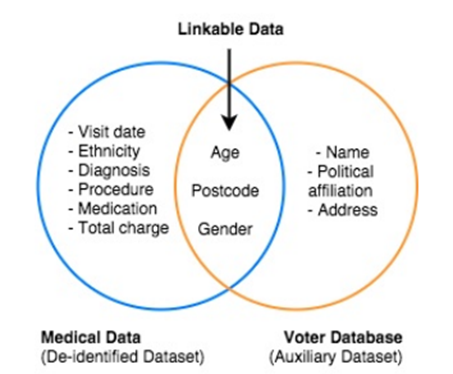
Bank Client Identifying Data – Draft reviewed with Jaroslaw and Marcin, 95 % of CID cases covered with the examples (May 6),

Detecting Personal Data within API Communication Using Deep Learning | by Gianluca Brigandi | Towards Data Science

Stat-Spotting: A Field Guide to Identifying Dubious Data: Best, Joel: 9780520279988: Amazon.com: Books

Identifying Specific Data Needs - Data Module #3 - Finding & Collecting Data for Your Research - All Guides at Macalester College