
Data Mining: Random Swapping based Data Perturbation Technique for Privacy Preserving in Data Mining | Semantic Scholar

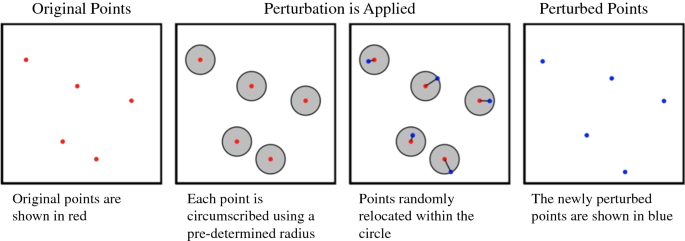
Data perturbation schemes to support multi-level privacy-preserving... | Download Scientific Diagram
Data Mining: Random Swapping based Data Perturbation Technique for Privacy Preserving in Data Mining
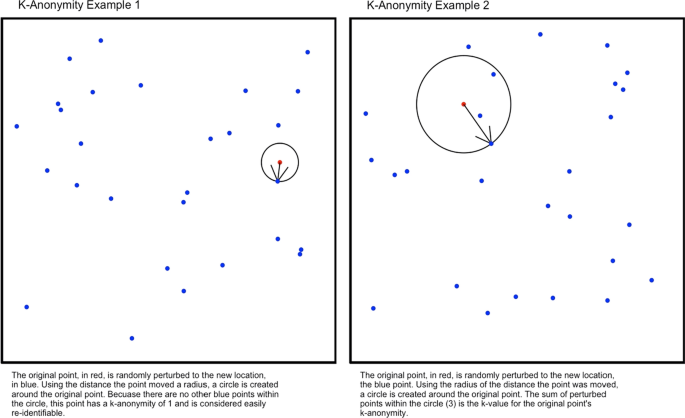
Measuring the impact of spatial perturbations on the relationship between data privacy and validity of descriptive statistics | International Journal of Health Geographics | Full Text

Mathematics | Free Full-Text | Evaluating the Privacy and Utility of Time-Series Data Perturbation Algorithms

Privacy preserving data mining through the time-series data perturbation. | Download Scientific Diagram

Multiplicative Data Perturbations. Outline Introduction Multiplicative data perturbations Rotation perturbation Geometric Data Perturbation Random. - ppt download
Measuring the impact of spatial perturbations on the relationship between data privacy and validity of descriptive statistics | International Journal of Health Geographics | Full Text











![Data Perturbation or Swapping [Series#2: I am Data!] Data Perturbation or Swapping [Series#2: I am Data!]](https://media.licdn.com/dms/image/C5612AQF6Q0C9n8wUIg/article-cover_image-shrink_600_2000/0/1648502191601?e=2147483647&v=beta&t=K1dK71j8v9DVuvq3mSqk2MAY13LZ56aiL1j61e0QgU0)




