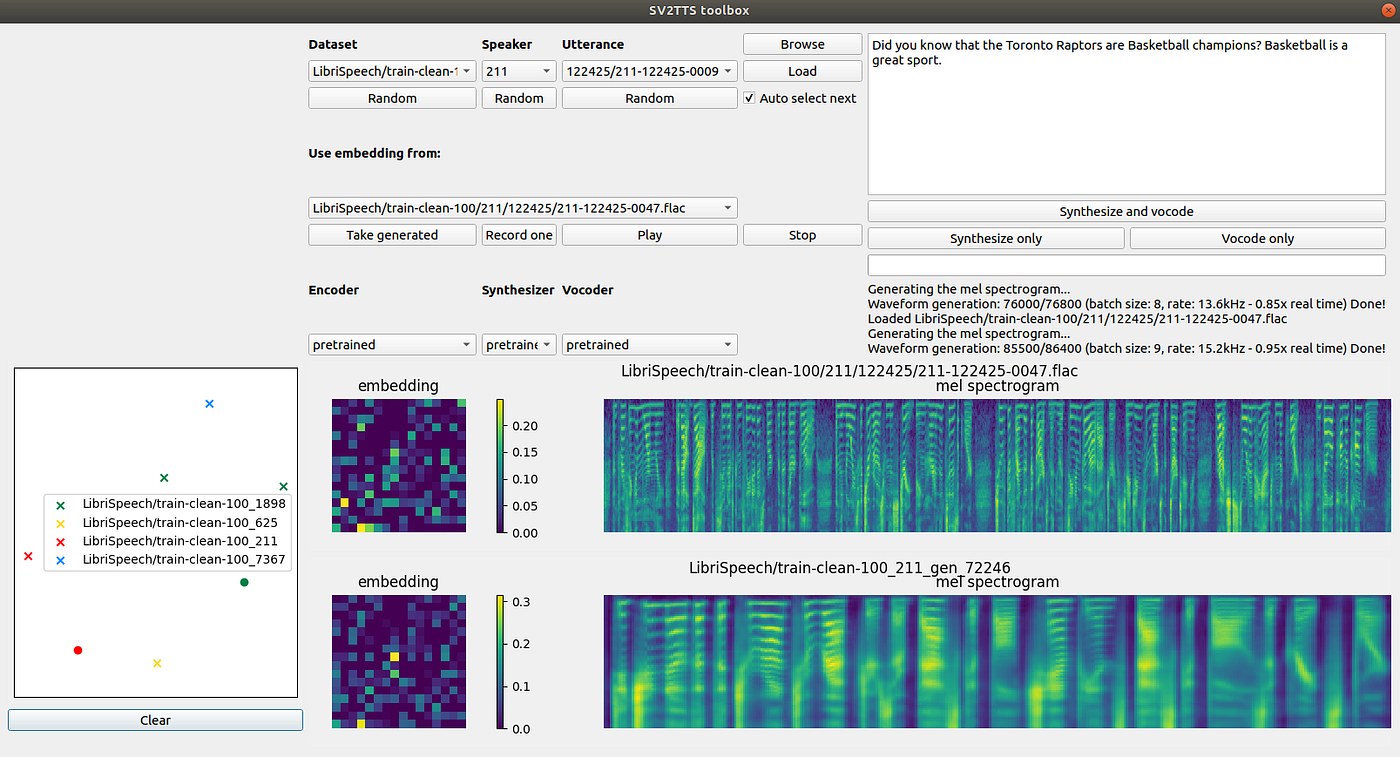
You can now speak using someone else's voice with Deep Learning | by George Seif | Towards Data Science
You can now speak using someone else's voice with Deep Learning | by George Seif | Towards Data Science

이와이엘 - EYL Inc. - The First Quantum Security at Your Fingertip Random numbers are used as the foundation in many areas of security, which include encryption, authentication, signing, key wrapping and
Amazon.com: Toysmith Tech Gear Multi Voice Changer, Amplifies Voice With 8 Different Voice Effects, For Boys & Girls Ages 5+, Colors vary : Musical Instruments

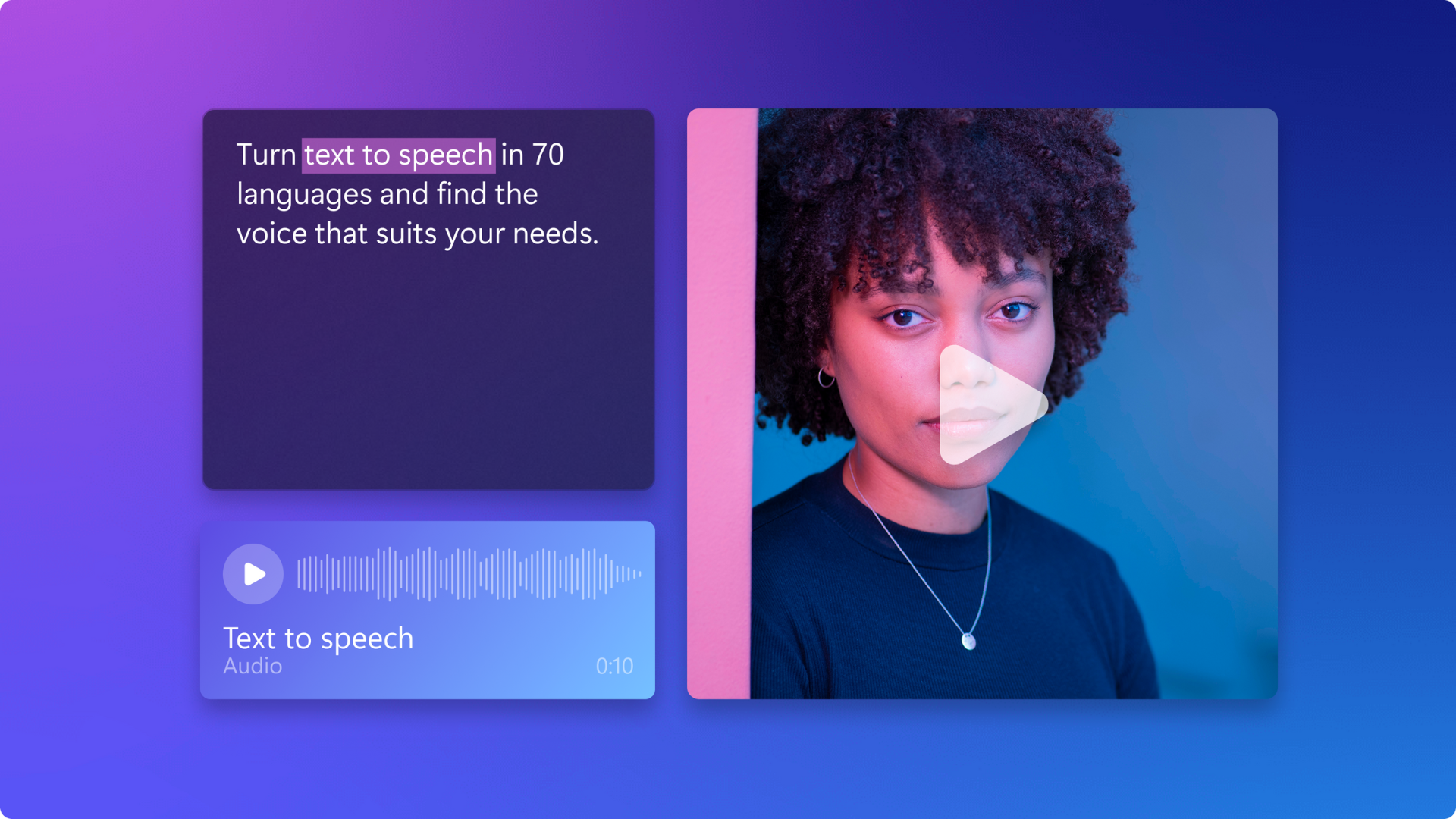
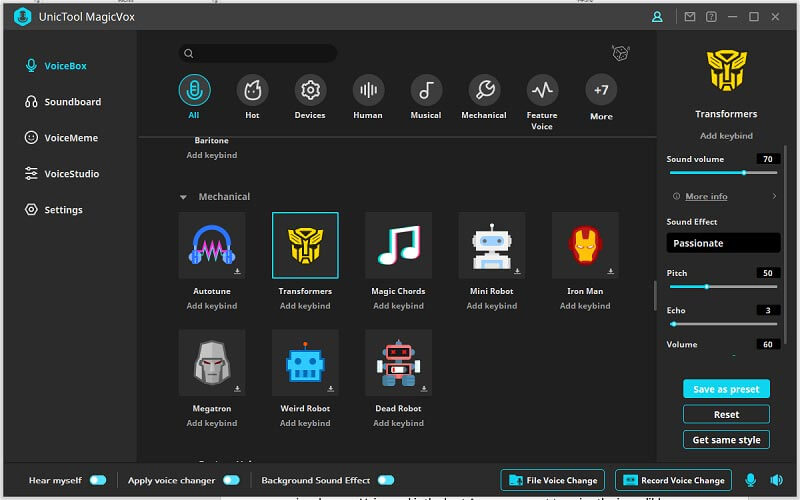
![Best 9 AI Voice Generators That Will Save Your Day[2022] Best 9 AI Voice Generators That Will Save Your Day[2022]](https://images.wondershare.com/filmora/article-images/8-robot-ai-voice-generator.jpg)

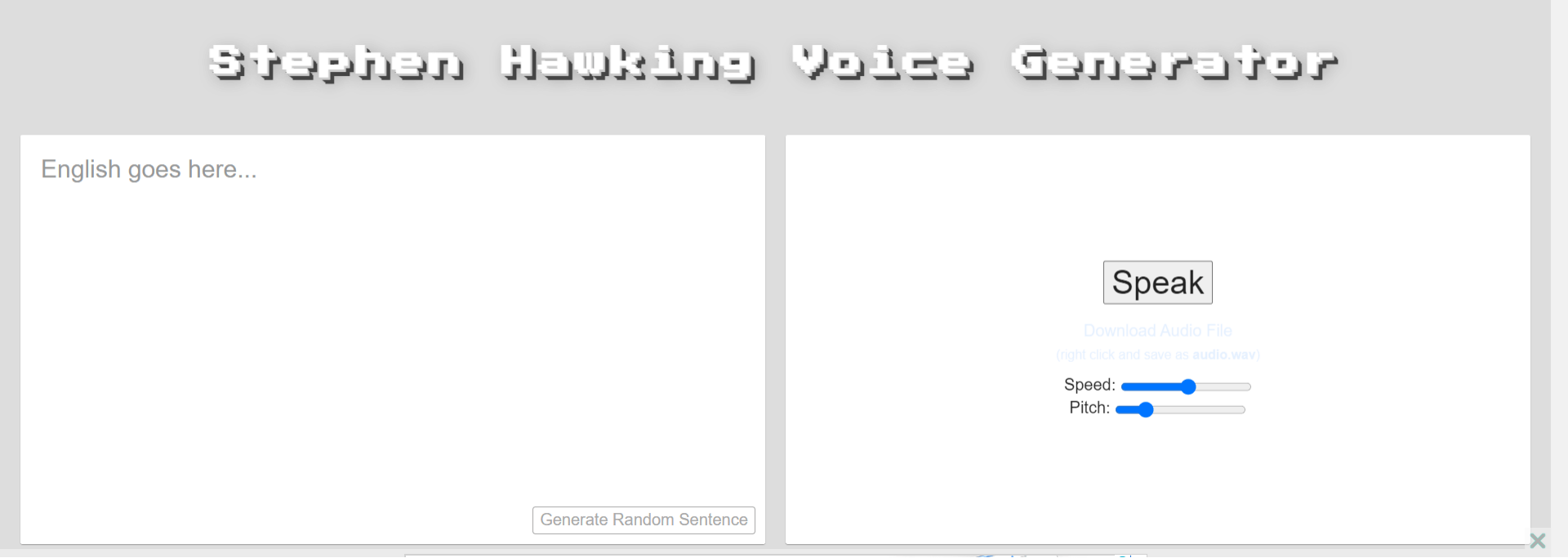
![9 Free Voice Generators Online-Generate Voice from Text [2022] 9 Free Voice Generators Online-Generate Voice from Text [2022]](https://images.wondershare.com/filmora/article-images/1-voice-generator-io.jpg)

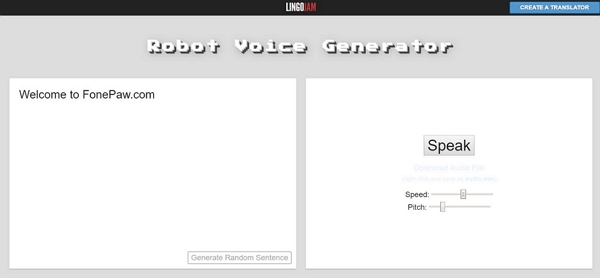



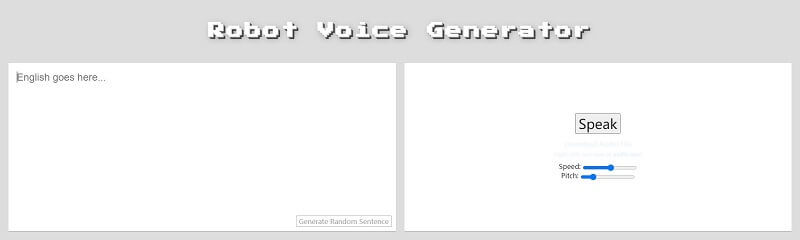

![9 Free Voice Generators Online-Generate Voice from Text [2022] 9 Free Voice Generators Online-Generate Voice from Text [2022]](https://images.wondershare.com/filmora/article-images/2022/07/mediaio-voice-generator.jpg)


